Lightweight security architecture for resource-constrained IoT devices: design patterns and implementation trade-offs
Keywords:
Lightweight cryptography, Internet of Things, Resource-constrained devices, Distributed authentication, Security design patternsAbstract
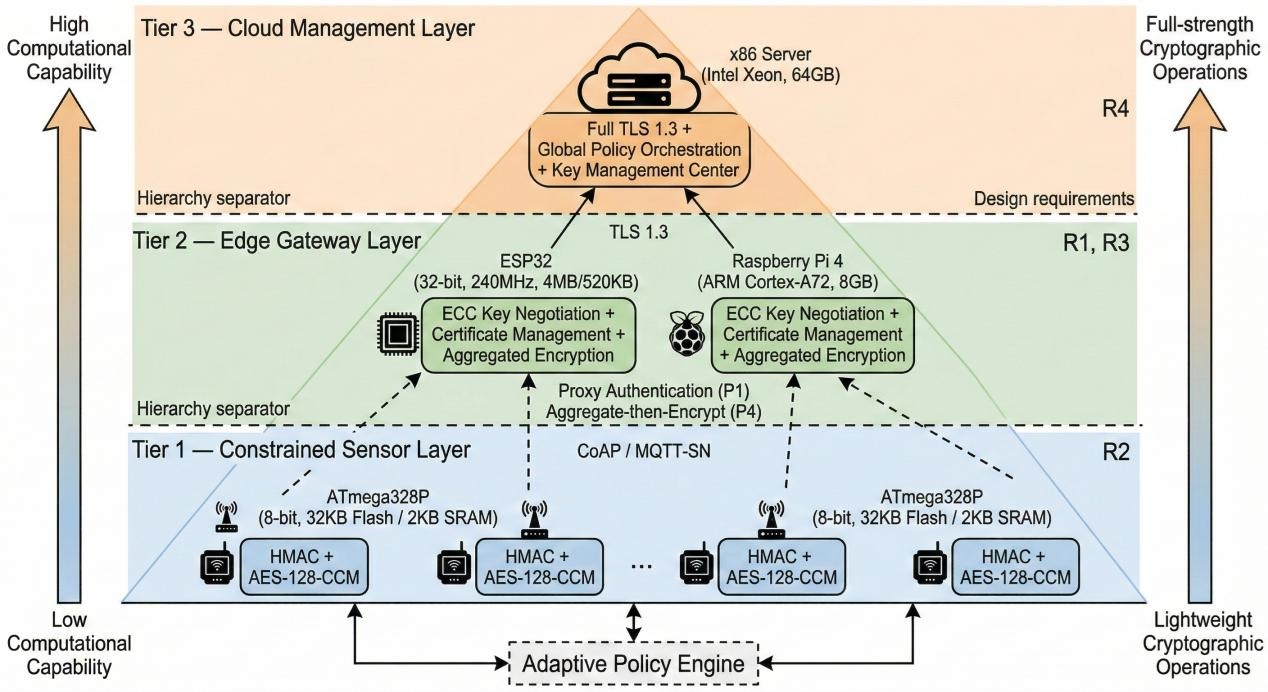
Securing large-scale IoT deployments poses fundamental challenges as traditional cryptographic protocols impose computational overhead that resource-constrained devices cannot sustain while maintaining real-time responsiveness. This paper systematically analyzes the design space of lightweight security architectures for IoT management systems, identifying critical tradeoffs between protection strength, computational efficiency, and operational scalability. Through iterative prototype development and performance profiling across heterogeneous device platforms, we derive a set of validated design patterns that balance security requirements with resource constraints. The proposed architecture employs stratified security policies in which protection mechanisms adapt to device capabilities—resource-rich gateways handle computationally intensive operations, while resource-constrained sensors implement optimized authentication protocols. A novel contribution is a distributed authentication framework that uses Merkle-DAG structures to achieve high transaction throughput without incurring blockchain consensus overhead, thereby enabling real-time coordination among thousands of devices. The paper also introduces a taxonomy of attack vectors specific to collaborative IoT management and evaluates defensive mechanisms through systematic penetration testing. Implementation guidelines address practical considerations, including key distribution in dynamic device populations, secure firmware updates over unreliable networks, and privacy-preserving data aggregation at edge nodes. Experimental results from laboratory testbeds and pilot deployments demonstrate that carefully optimized classical cryptographic primitives can provide adequate security for current IoT systems without incurring prohibitive overhead, while the modular architecture supports future migration to post-quantum algorithms as hardware capabilities improve. This work provides system architects with evidence-based design principles for implementing security in resource-constrained distributed systems where traditional approaches prove infeasible.
References
J. S. Yalli, M. H. Hasan, and A. Badawi, "Internet of things (IoT): Origin, embedded technologies, smart applications and its growth in the last decade," IEEE Access, vol. 12, pp. 91357–91382, 2024. [Online]. Available: https://ieeexplore.ieee.org/document/10570411
M. Gelgi, Y. Guan, S. Arunachala, M. S. S. Rao, and N. Dragoni, "Systematic literature review of IoT botnet DDoS attacks and evaluation of detection techniques," Sensors, vol. 24, no. 11, Art. no. 3571, 2024. [Online]. Available: https://www.mdpi.com/1424-8220/24/11/3571
G. Restuccia, H. Tschofenig, and E. Baccelli, "Low-power IoT communication security: On the performance of DTLS and TLS 1.3," in Proc. 9th IFIP/IEEE Int. Conf. Performance Evaluation of Wireless Ad Hoc, Sensor, & Ubiquitous Networks (PEMWN), Berlin, Germany, 2020, pp. 1–6. [Online]. Available: https://ieeexplore.ieee.org/document/9293085
S. U. Jan, S. Ahmed, V. Shakhov, and I. Koo, "A survey and ontology of blockchain consensus algorithms for resource-constrained IoT systems," Sensors, vol. 22, no. 21, Art. no. 8188, 2022. [Online]. Available: https://www.mdpi.com/1424-8220/22/21/8188
M. N. Khan, A. Rao, and S. Camtepe, "Lightweight cryptographic protocols for IoT-constrained devices: A survey," IEEE Internet of Things Journal, vol. 8, no. 6, pp. 4132–4156, 2021. [Online]. Available: https://ieeexplore.ieee.org/document/9246541
National Institute of Standards and Technology, "Ascon-based lightweight cryptography standards for constrained devices: Authenticated encryption, hash, and extendable output functions," NIST Special Publication 800-232, Gaithersburg, MD, USA, 2025. [Online]. Available: https://csrc.nist.gov/pubs/sp/800/232/final
M. S. Turan, K. McKay, D. Chang, and L. E. Bassham, "Status report on the final round of the NIST lightweight cryptography standardization process," NISTIR 8454, National Institute of Standards and Technology, 2023. [Online]. Available: https://nvlpubs.nist.gov/nistpubs/ir/2023/NIST.IR.8454.pdf.
D. Garcia-Carrillo and R. Marin-Lopez, "Lightweight CoAP-based bootstrapping service for the Internet of Things," Sensors, vol. 16, no. 3, Art. no. 358, 2016. [Online]. Available: https://www.mdpi.com/1424-8220/16/3/358
Y. Liu, J. Peng, J. Kang, A. M. Iliyasu, D. Niyato, and A. A. A. El-Latif, "A secure federated learning framework for 5G networks," IEEE Wireless Communications, vol. 29, no. 4, pp. 68–75, 2022. [Online]. Available: https://ieeexplore.ieee.org/document/9705048
D. Berdik, S. Otoum, N. Schmidt, D. Porter, and Y. Jararweh, "A survey on blockchain for information systems management and security," Information Processing & Management, vol. 58, no. 1, Art. no. 102397, 2021. [Online]. Available: https://www.sciencedirect.com/science/article/pii/S0306457321001795
OWASP Foundation, "OWASP Internet of Things Top 10 2024," 2024. [Online]. Available: https://owasp.org/www-project-internet-of-things/
V. Hassija, V. Chamola, V. Saxena, D. Jain, P. Goyal, and B. Sikdar, "A survey on IoT security: Application areas, security threats, and solution architectures," IEEE Access, vol. 7, pp. 82721–82743, 2019. [Online]. Available: https://ieeexplore.ieee.org/document/8742568
E. Daniel and F. Tschorsch, "IPFS and friends: A qualitative comparison of next generation peer-to-peer data networks," IEEE Communications Surveys & Tutorials, vol. 24, no. 1, pp. 31–52, 2022. [Online]. Available: https://ieeexplore.ieee.org/document/9714765
B. Chatterjee, D. Das, S. Maity, and S. Sen, "RF-PUF: Enhancing IoT security through authentication of wireless nodes using in-situ machine learning," IEEE Internet of Things Journal, vol. 9, no. 12, pp. 9066–9081, 2022. [Online]. Available: https://ieeexplore.ieee.org/document/9576600
OWASP Foundation, "OWASP IoT Security Testing Guide," 2023. [Online]. Available: https://owasp.org/owasp-istg/